Founders build. We clear the path.
We support you across the entire lifecycle.
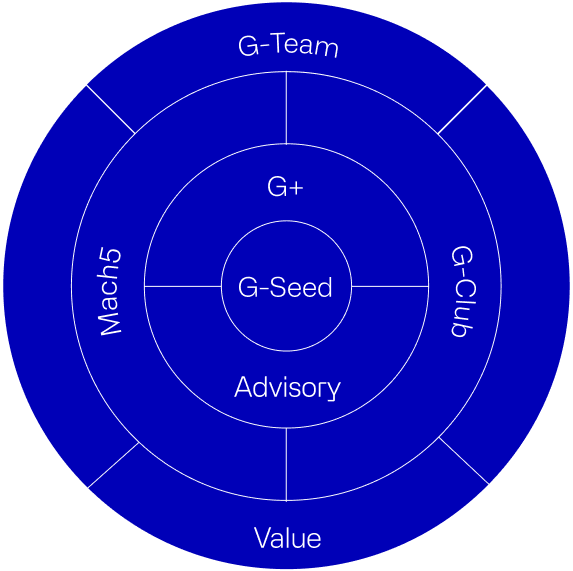
We built a full framework to back founders from seed to market leadership. One clear path with the right tools, people, and momentum.G-Seed starts it. G+ scales it. Mach5 accelerates it. G-Club surrounds it.Focused on Cybersecurity and AI, Glilot brings hands-on experience, flexible capital, and a global network that delivers results. We cover every stage with real, hands-on support.
G-Seed
Backs founders from first spark to scale. Early, deep, aligned.
G+
For founders ready to scale. Leads A/B rounds toward growth and dominance.
Exclusive wealth management for tech founders.
Value
We support founders with practical value, wrapping them with professional support from every possible type needed.
Five rounds of customer insight to hit product-market fit fast.
Fast access to top industry minds.
A VC that is deeply aligned with you - yep, that exists.
I love the Glilot team. They're incredibly professional.
Name:
Rotem Iram
Position:
CEO of At-Bay
Glilot helped us with every possible challenge, such as opening doors, hiring, and providing insights.
Name:
Daniel Krivelevich
Position:
CTO of Cider Security
Glilot is one of the most amazing VCs in cyber security.
Name:
Shay Morag
Position:
CEO of Ermetic
Glilot is founder-friendly and here to support founders and companies.
Name:
Yoav Levy
Position:
CEO of Upstream Security
Akamai Technologies has announced that it has entered into a definitive agreement to acquire Israeli browser-based AI usage control and secure enterprise browser company LayerX for $205 million
CopilotKit first came to our attention not through a pitch, but through something we pay close attention to as a fund: organic developer adoption. We regularly track emerging open-source projects gaining traction in developer communities, and CopilotKit’s growth curve stood out, developers were pulling it into their stacks, raving about the simple yet powerful new layer for agent-to-user interactions, and the project’s growth pace suggested it was solving a real and urgent problem.
When we met co-founders (and brothers) Atai and Uli Barkai, we were immediately struck by their clarity of vision for agentic-human interfaces in an AI-powered world. But what truly set CopilotKit apart was the speed at which they turned open-source momentum into a commercial business, always the hardest challenge for developer-first companies. Within months, Fortune 500 enterprises were paying meaningful dollars for CopilotKit’s early enterprise offering, and revenue was growing rapidly. It’s one thing to build something developers love. It’s another entirely to make that love monetizable. CopilotKit did both, remarkably fast.
Agents Need a New User-Interface Layer
For the past decade, software interfaces followed a simple model: a frontend talks to a backend, the backend replies with data, the frontend renders the reply. A stateless ping-pong, no persistence, no learning, no adaptation. AI agents break that model entirely. They stream responses, pause for human input, resume across sessions, generate dynamic UI elements on the fly, and orchestrate complex multi-step workflows. They produce continuous, stateful, interactive experiences, and the old frontend stack simply wasn’t built for any of that.
Every company embedding AI agents into its products today is discovering the same thing: the hardest part isn’t building the agent, it’s building the interaction layer between the agent and the human user, while avoiding lock-in to a specific agentic backend framework. How does the agent surface its work? How does the user steer, correct, or approve? How does this all persist across sessions, devices, and workflows? And how does the organization track and analyze user interactions with agents? Before CopilotKit, teams were forced to reinvent this layer from scratch – every time, for every frontend, and with every agentic backend they use, at enormous cost and with limited results.
AG-UI and the CopilotKit Stack
What we loved about CopilotKit was their insight that the agent-to-user interface is not an application problem ,it’s an infrastructure problem. Just as MCP became the universal standard for connecting agents to external tools, CopilotKit is building the equivalent standard for connecting agents to users.
At the core of this is AG-UI, an open protocol created by CopilotKit that defines how agentic backends communicate with modern frontends. AG-UI is the third leg of what is becoming the agentic protocol stack: MCP connects agents to existing software tools, A2A interconnects agents between themselves, and AG-UI connects these agents to human users. Instead of every application building its own bespoke agent-user interface, AG-UI provides a universal language, each backend framework implements the protocol once, and all applications can then work independently of the backend with a rich agentic user experience.
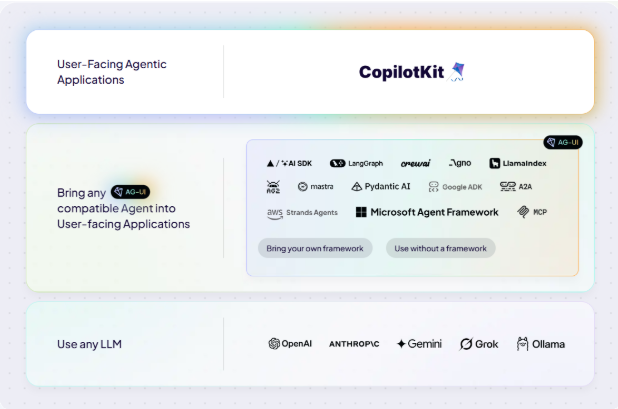
The ecosystem’s response was extraordinary. Google, Microsoft, Amazon, and Oracle have all integrated AG-UI into their own agent frameworks, and officially endorsed CopilotKit for enterprises building agentic products. Leading open-source agent frameworks, LangChain, LlamaIndex, Mastra, PydanticAI, Agno, have aligned to and implemented the AG-UI protocol. In a fragmented, fast-moving ecosystem where standards rarely emerge this early, CopilotKit has become the neutral, trusted layer for agent-user interaction that everyone is building on. That kind of ecosystem convergence is rare, and it doesn’t happen by accident. We were sold.
Why Glilot+? Why Now?
At Glilot, we’ve spent over a decade investing in the infrastructure layers that define how enterprises build and secure software, from cybersecurity and cloud infrastructure to developer tools and DevOps. CopilotKit sits squarely at the intersection of these themes. It’s not an AI application; it’s the infrastructure that enables every AI application to interact with its users. That distinction matters, because infrastructure compounds in ways that applications don’t.
We also made a deliberate bet on timing. The agentic era is arriving faster than most enterprises are prepared for, and CopilotKit is giving them the building blocks to ship agent-powered products without reinventing a critical layer of the new agentic stack. The rare combination of rapid open-source adoption and an enterprise offering that converted into meaningful revenue almost immediately signals genuine product-market fit, not just developer enthusiasm, making this investment a perfect fit for Glilot+.
We’re proud to lead CopilotKit’s $27M Series A alongside our colleagues from NFX and SignalFire, and support the company’s fast growth across the US and globally. Atai, Uli, and the entire CopilotKit team are building what we believe will become a foundational infrastructure layer of the software stack for years to come, and we couldn’t be more excited to be part of this journey.